I'm looking for some help with accessing my VPN over tor. A little background..
I have a router at home that I can connect to which routes all of my traffic over tor. The router uses port 9030. My VPN is hosted on DigitalOcean. Using OpenVPN on an Ubuntu 14.04 droplet. I'm using tunnelblick to access my VPN. I'm also using uncomplicated firewall (ufw) on my VPN on DigitalOcean.
Here's the issue; I've tried opening port 9030, 9040, 9001 etc. on my firewall for my VPN but tunnelblick's status just says "Waiting for authorization from server" and never gets any response back. I think it's my firewall but when I checked the firewall logs I can never find the exit node IP that connects to the VPN.
Any ideas on what to check for in configuration files (in OpenVPN config, tunnelblick config etc.) would be very helpful.
Thanks
EDIT: Following are my config files and torrc
torrc for Onion Pi https://gist.github.com/dhurley14/8d4b8d8ac98d74b1e665
torrc for DigitalOcean VPN https://gist.github.com/dhurley14/264754ff2eafb844ad9b
UPDATE 2:
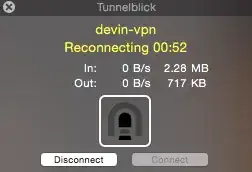
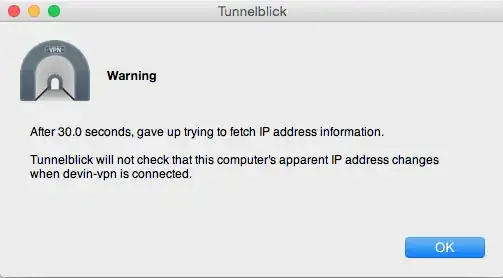
This is what tunnelblick tells me when I try to connect to the VPN from my Onion Pi Access Point. I changed the client and server config to allow for TCP connections and updated the firewall to allow tcp connections on port 9001. I also ran the three commands in the terminal. Getting closer I think.